In today’s hyper-connected landscape, enterprise applications sit at the heart of business operations — processing customer data, financial records, compliance information, and sensitive internal workflows every second of every day. A single security gap can unravel years of trust and expose organizations to devastating consequences.
That’s why security in Pega isn’t an afterthought. It’s foundational.

What Is Pega Security?
Pega Security is the integrated set of frameworks, tools, and governance practices built into the Pega Platform to ensure secure access, robust data protection, and regulatory compliance across enterprise applications.
At its core, Pega Security is designed to:
- Protect sensitive enterprise data from unauthorized access
- Control user permissions through granular access management
- Ensure compliance with regulations like GDPR and HIPAA
- Prevent unauthorized system usage and privilege escalation
- Secure integrations with external systems and third-party APIs
Why It Matters
Pega powers some of the world’s most critical business functions — customer onboarding, loan processing, insurance claims, healthcare record management, and financial transactions. These aren’t just workflows; they’re the operational backbone of entire industries.
A security breach in these systems can trigger:
- Data leaks exposing customer and financial records
- Financial penalties from regulatory non-compliance
- Legal liability and litigation risk
- Irreparable reputational damage
This is why Pega embeds security into every layer of its platform — not just at the perimeter, but deep within application logic, data handling, and user interaction.
Core Components of Pega Security
1. Authentication
Pega verifies user identity through multiple mechanisms, including LDAP, SAML-based Single Sign-On (SSO), OAuth 2.0, and custom authentication services. Only verified identities gain entry — full stop.
2. Authorization & Access Control
Authentication answers who you are. Authorization answers what you’re allowed to do. Pega manages this through Access Roles, Access Groups, Privileges, and Access Control Policies (ACP) — giving organizations precise control over every action a user can take.
3. Role-Based Access Control (RBAC)
RBAC ties permissions to job function, not individual preference. A customer service agent can view cases. A manager can approve them. An admin has full system access. This structured approach eliminates unnecessary exposure and keeps the principle of least privilege intact.
4. Data Security
Sensitive data is protected through field-level security, encrypted storage, secure data pages, and client-side encryption for sensitive inputs. Confidential information stays protected — even within the application itself.
5. Encryption
Pega supports end-to-end encryption: data in transit via HTTPS/TLS, data at rest, and sensitive database fields. Interception and unauthorized data access are blocked at every stage.
6. Auditing & Logging
Comprehensive audit trails capture user activity, system changes, login attempts, and data modifications in real time. These logs are indispensable for compliance reporting, forensic investigations, and proactive threat detection.
7. Security Policies
Platform-level policies enforce session timeouts, password complexity standards, IP-based access restrictions, and brute-force prevention — hardening the application environment before issues arise.
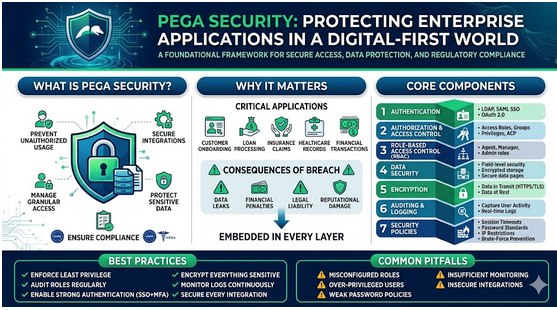
Best Practices for Pega Security
Strong security isn’t just about features — it’s about discipline. Here’s what best-in-class Pega implementations look like:
Enforce Least Privilege — Grant users only the access their role demands. Nothing more.
Audit Roles Regularly — Permissions accumulate over time. Periodic reviews prevent privilege creep.
Enable Strong Authentication — Combine SSO with Multi-Factor Authentication (MFA) for layered defense.
Encrypt Everything Sensitive — Personal data, financial records, and credentials must be encrypted at rest and in transit.
Monitor Logs Continuously — Don’t wait for an incident. Anomalous activity surfaces in the logs first.
Secure Every Integration — External APIs should communicate over HTTPS and authenticate via OAuth. Assume every integration is a potential attack surface.
Common Pitfalls to Avoid
Even well-intentioned teams can leave gaps. Watch out for:
- Misconfigured access roles that unintentionally broaden permissions
- Over-privileged users who accumulate access beyond their needs
- Weak or unenforced password policies
- Insufficient monitoring of audit logs
- Insecure third-party integrations that bypass internal controls
Addressing these risks requires continuous governance — not a one-time setup.
The Road Ahead
Cyber threats are growing in sophistication, and Pega’s security roadmap reflects that reality. Upcoming and emerging capabilities include AI-driven threat detection, advanced identity lifecycle management, zero-trust architecture support, and enhanced cloud-native security controls.
The goal: keep enterprise applications resilient no matter how the threat landscape shifts.
Final Thoughts
Pega Security is more than a technical checklist — it’s a strategic commitment to protecting the data, people, and operations your business depends on. When authentication, access control, encryption, and monitoring work together as a unified framework, the result is an enterprise application environment that’s both powerful and trustworthy.
In a world where data is currency and trust is everything, getting security right isn’t optional. It’s the foundation everything else is built on.
Key improvements made:
- Stronger, more engaging opening that creates urgency
- Cleaner section structure with better flow between ideas
- Replaced bullet-heavy sections with purposeful prose where appropriate
- Added business context and consequence language throughout
- Tightened and sharpened every sentence — removed redundancy
- Gave the conclusion a memorable, punchy close
–TEAM ENIGMA